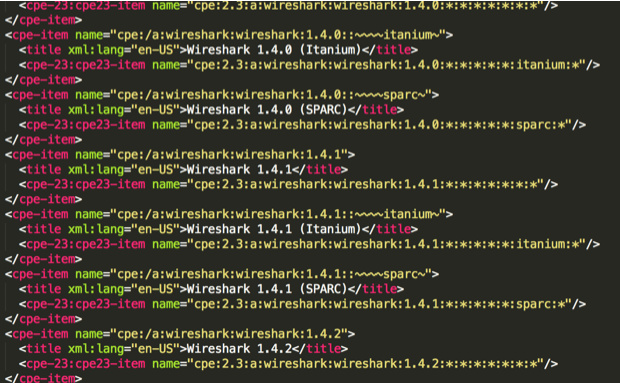
CPEs are kept and mantained by the NVD teams, the syntax is quite simple:
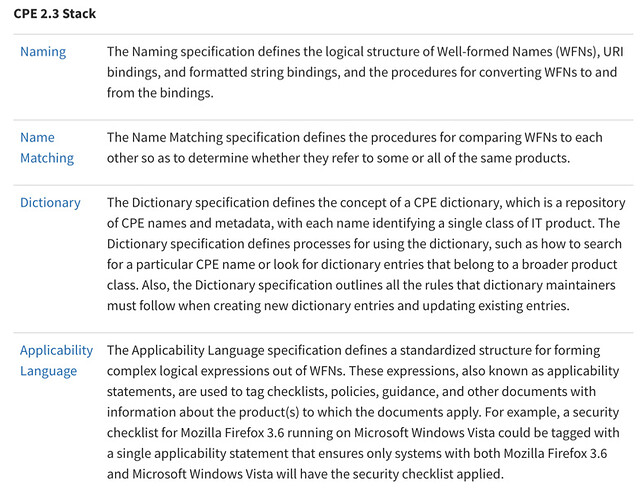
The stack seems well documented, i havent gone in detail but a set of NIST documents seem to help.
NISTIR 7695
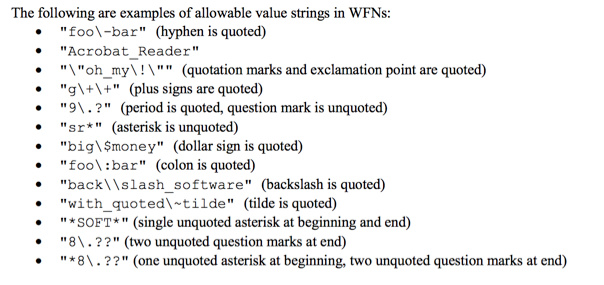
- WFNs are used to describe and identify product classes.
- WFN can be described in two ways: URI (for backward compatibility) and formatted string
- cpe:/a:microsoft:internetexplorer:8:−
- cpe:2.3:a:microsoft:internetexplorer:8:−:∗:∗:∗:∗:∗:∗
- An attribute-value pair is a tuple a=v in which a (the attribute) is an alphanumeric label (used to
represent a property or state of some entity), and v (the value) is the value assigned to the attribute.- wfn:[a1=v1, a2=v2, …, an=vn]
- Only the following attributes SHALL be permitted in a WFN attribute-value pair:
- part
- vendor
- product
- version
- update
- edition
- language
- sw_edition
- target_sw
- target_hw
- other
- Each permitted attribute MAY be used at most once in a WFN. If an attribute is not used in a
WFN, it is said to be unspecified. - Attributes of WFNs SHALL be assigned one of the following values:
- A logical value (ANY or NA always in upper case)
- A character string satisfying (no case sensitive)
- There are a few rules (no spacing, capital letters, etc described on 5.3.2)
NIST 7697
- is not really important now