Question: Need assist with SAML connector related error. I’ve exhausted all the resources I could find.
More information:
- Running the most recent version of Eramba Community on Azure VM with Docker
- I first followed the directions published in 2021 (in text form) from this site and was unable to successfully connect.
- Following that I found the YouTube video produced by Eramba in 2022 regarding the SAML connector. I started over, followed it to the letter and continued to get the exact same error.
- I found all the tips, pointers, etc out there and ensured that all of that was applied…still the same error.
So now I am asking for help.
Attachments:
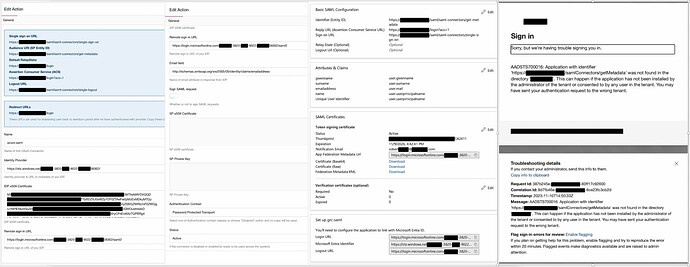
Screenshot 1/2 is my configuration in Eramba SAML connector redacted for privacy.
Screenshot 3 is my Azure application configuration redact for privacy.
Screenshot 4 is the actual error I get when I try to login via SAML with a known user.
Related to login, I can successful see the SAML button on the login page, I click that and it correctly takes me to the tenant I am trying to authenticate against and presents Microsoft username prompt, then password prompt…and then I get the error shown in Screenshot 4.
Any guidance would be greatly appreciated…I am out of ideas.
Thank you
Robert
**Had to combine all screenshots to one b/c the system won’t let my upload more than one. Hopefully its still legible.